How can Artificial Intelligence help in cyber security?
Cyber security is a major challenge in modern business operations.
While technology has helped businesses become more effective and achieve higher productivity, it has also empowered cybercriminals who use emails and other channels to launch cyberattacks that cost businesses billions annually.
In 2020, Cybersecurity Ventures predicted that by 2025, the cost of global cybercrime will reach $10.5 trillion up from $3 trillion in 2015. The financial implications of cybercrime across the globe are dire and will continue getting worse unless better solutions are created.
Artificial intelligence has the potential to significantly improve the war on cybercrime. It can be used to reinforce cybersecurity best practices and minimize cyber threats through real-time monitoring and early detection of attacks.
In addition, AI can be trained to understand cybersecurity threats well and provide protection against more advanced threats.
To understand these claims in-depth, let’s go through 5 main applications of artificial intelligence in cyber security.
1. Threat Detection
Businesses face cyber threats every day. They are perfect targets for financially motivated cybercriminals and disgruntled former employees.
To protect themselves, they must implement the latest threat detection systems. Often, they include antivirus in their arsenal for threat combat. Essentially, antiviruses scan files for known malware signatures and quarantine files that turn out positive.
The challenge with this mechanism is that antiviruses have to be updated regularly to keep up with malware upgrades to provide ultimate protection. Yet according to AV-Test Institute, over 450000 new malwares are detected every day.
Imagine the kind of work security solutions developers have to put in to ensure an antivirus is up to date with the latest threats.
One of the most significant artificial intelligence applications in cybersecurity is in advanced threat detection. Unlike traditional signature-based threat detection systems, AI-based threat detection involves the observation of abnormal behavior.
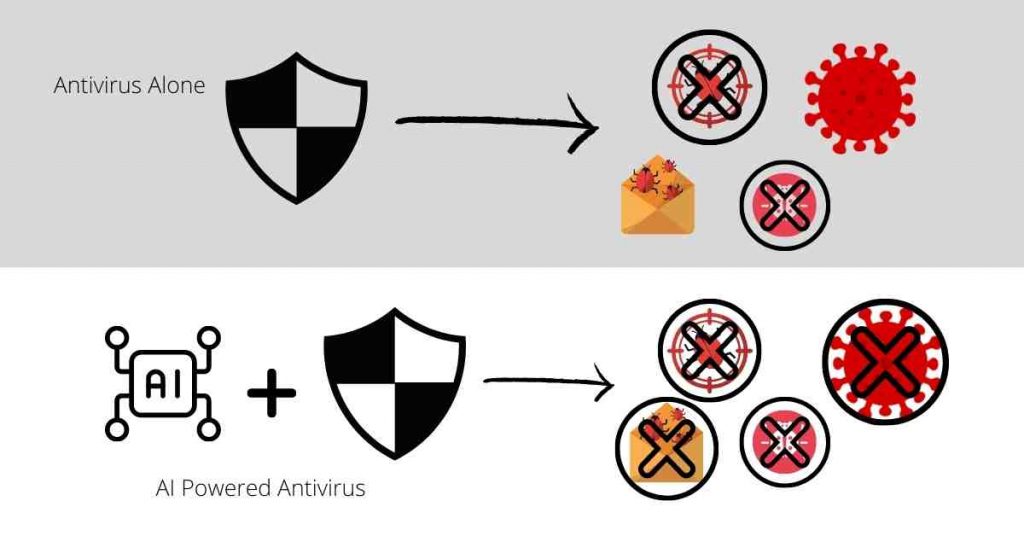
AI enables a security software to think like a hacker and thus detect vulnerabilities that cybercriminals would normally exploit. In addition, it can detect weaknesses in your devices and alert you before a threat has occurred so you can take precautionary measures.
When paired with a traditional threat detection system, you increase the probability of detecting more threats with great accuracy. You can also include a robust VPN service like ExpressVPN to add an extra layer of security.
By doing so, you would have implemented one of the most effective applications of artificial intelligence techniques to combating cybercrime.
A US-based healthcare service provider deployed an AI-powered threat detection system to augment its existing antivirus. The new system immediately detected and blocked 3 custom-designed malware which the traditional antivirus wouldn’t identify.
The company also realized a lower performance impact of each endpoint and increased monetary benefit for consolidating their antivirus solution
2. Improving Authentication
Cyber threats occur when unauthorized persons gain access to a control system device or the network through a data communication pathway.
For businesses, authentication can be a big challenge.
Knowing whether the connection requests into the system are legitimate or not requires constant monitoring by full-time network managers especially in large companies which generate thousands of requests.
It is also challenging to know if suspicious login activities are the works of insiders or outsiders.
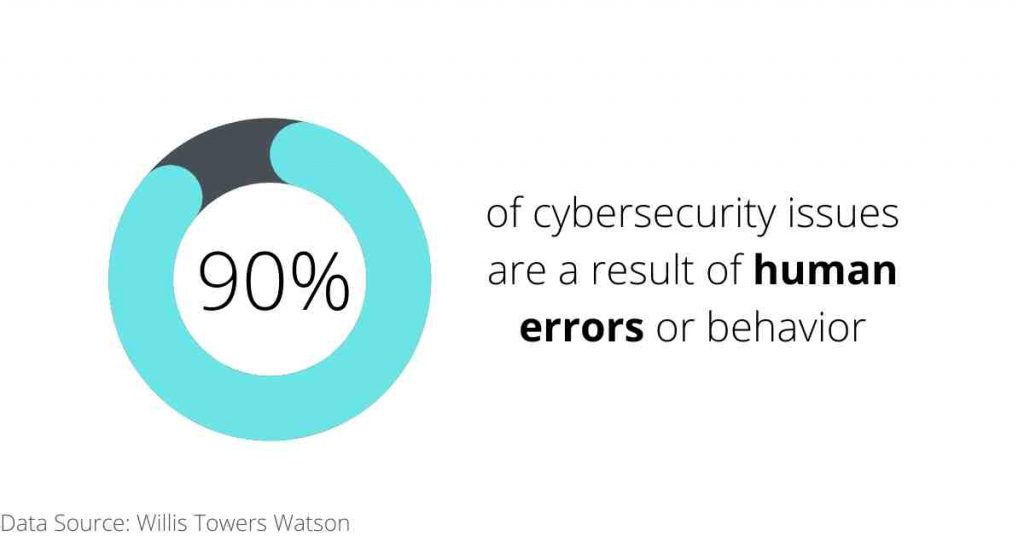
Humans are limited in terms of efficiency, working hours, and accuracy. In fact, a study by Willis Towers Watson found that 90% of cybersecurity issues originate from human error. Hence, depending solely on them to provide authentication services can be risky.
One of the most significant applications of machine learning in cyber security is in improving authentication.
AI-backed authentication technologies analyze individual factors about login attempts to come up with a risk score for a scenario. For instance, it can flag a user attempting to log in from certain IP addresses in the middle of the night. Check out some of the best VPN services that can protect your dedicated and static IP addresses.
In addition, by using neural networks which imitate the human brain and adapt through exposure to datasets with correct results, the system develops better algorithms to determine factors that indicate an attack.
Lastly, to reduce incidences of false positives, the AI system can allow users with low-risk scores to log in faster by not requiring security authentication like fingerprint scans.
Orderbird, a point of sale system solutions provider implemented OneLogin to support its authentication system for employees. Courtesy of this change, the company streamlined the authentication of new employees as it eliminated the need to remember passwords
In addition, Orderbird can rest easy knowing that departing employees won’t have access to their resources.
3. Faster Threat Response
Cyber security threats are growing in numbers and sophistication. Today, businesses face the huge task of staying ahead of these threats and are using tools at their disposal to do so.
But they face numerous challenges because of a high amount of manual efforts required to stay afloat with threat response. For instance, most security teams lack full visibility into network traffic and thus don’t see most threats.
Despite the dire consequences of cyber threats, 22% of organizations have limited resources to respond to a security incident according to a BAE Systems survey.
During threat responses, you need to review, interpret and understand thousands of alerts sent daily. You need to staff highly trained and expensive operators on a 24/7 basis for effective threat response.

Threat response is a major use of artificial intelligence in cyber security. AI-backed systems can offer better context for faster response to security alerts and elucidate root causes for vulnerability mitigation measures to be put in place.
Through smart threat modeling, AI can create predefined threat behavior models for quick identification and correlation with valid alerts. Then all network threats are automatically disrupted before spreading to other devices in the network.
A security analyst can then use enterprise-wide analytics to quickly prioritize severe threats and immediately direct them for response measures. In addition, consider adding to your arsenal a VPN with additional protection against cyber threats.
With such an effective and precise threat containment system, your security team will always be ahead of cyber threats.
Quickplay, a media content company needed a proactive cyber security solution that would discover security problems fast and stop suspicious activities.
By implementing Darktrace’s adaptive system, the company could monitor the network 24/7, get updates of real potential threats, and quickly swing into action to respond and avert the threats.
The media company implemented one of the most effective applications of artificial intelligence techniques to combat cybercrime which allowed employees to focus on service delivery.
4. Social Engineering Detection
Social engineering involves the manipulation of people’s psychologies to get them to reveal confidential information or take an action that places them in a vulnerable position.
In the recent past, social engineering attacks have become more frequent specific in their targets.
Cybercriminals are using artificial intelligence and machine learning tools to hack employees’ logins and gain access to business networks and systems.
According to a study by Verizon, 93% of successful data breaches are caused by social engineering attacks
Many users don’t know how real-looking AI-generated voice fakes and deepfakes are.
For instance, a CEO’s voice can be used to promote an upcoming phishing email which significantly increases the chances that employees will fall victim to the phishing.

Social engineering detection is one of the most impactful applications of machine learning in cyber security. AI-backed tools use advanced features to recognize fakes and label them as such so that employees can avoid them.
In addition, AI technology learns the real entity’s facial mannerism and uses this information to analyze a video in question and determine whether it’s genuine or a deepfake.
However, in order to achieve maximum social engineering detection, AI tools should be backed by a VPN that can detect phishing and cyber security awareness. Regular awareness training on new attacks can help your employees to be alert for social engineering tactics and to report upon detection.
Martin Engineering was experiencing an increase in spear-phishing attacks and despite measures such as employee training, they couldn’t achieve full containment of phishing attacks.
On deploying Graphus, an AI social engineering tool, the automated detection and realized it was 3 times more effective than they had thought.
Courtesy of Graphus, the company significantly improved phishing prevention, one of the main applications of artificial intelligence in cyber security, and could now concentrate on customer service.
5. Vulnerability Assessment
Security teams in every business often conduct vulnerability tests to check for outdated security systems, identify vulnerabilities and recommend mitigation measures.
They use vulnerability assessment tools that are designed to detect loopholes in legacy systems. However, these tools cannot identify vulnerabilities especially in new technologies such as IoT and hybrid environments.
In addition, they can only go as far as detecting vulnerabilities and listing them in no particular order.
Your security team will need to handle multiple vulnerabilities without context. They rarely know the risk level of each vulnerability to prioritize the most severe ones.
Considering that high-risk vulnerabilities exist within the network parameters of 84% of companies according to a study by Positive Technologies, you need a better vulnerability management system than traditional tools.
Enhanced vulnerability assessment is one of the best artificial intelligence applications in cybersecurity.
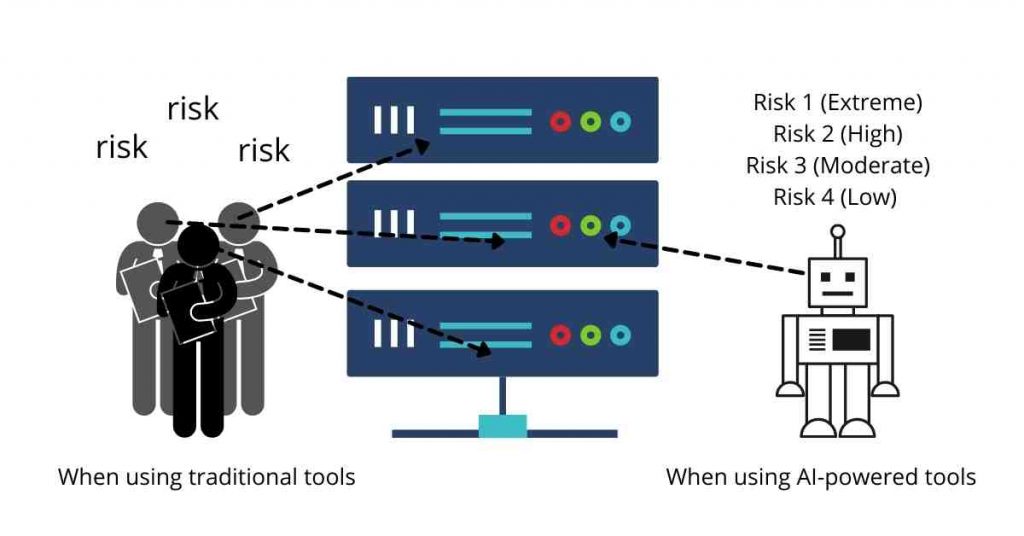
AI-powered vulnerability assessment tools can analyze data in real-time and prioritize vulnerabilities based on the risk level for security teams to act fast.
Using vulnerability detection features that can scan and predict risk across thousands of attack vectors and threats, you increase the chances of identifying many loopholes and the risk impact variations on your business.
AI technologies are good at detecting which assets are most valuable to a business.
Using user and event behavior analytics, they can detect anomalies that indicate unknown compromise, compare assets and establish a baseline for prioritizing vulnerability mitigation measures.
A large Midwest health system was able to significantly improve the detection of vulnerabilities by using the AI-powered security analytics system.
Besides, this particular use of artificial intelligence in cyber security could detect malware on medical devices which it isolated and remediate to avoid disruptive and costly breaches that could have threatened patient safety and privacy
Conclusion
Although artificial intelligence use in combating cybercrime is relatively new, it has tremendous capabilities that enhance life and business operations.
The 5 main applications of artificial intelligence in cyber security that we’ve discussed, already demonstrate how integral AI is in creating solutions to ensure cyber security.
As a business manager or security professional, you should stay updated on cyber security to get exposure to the best solutions for identifying and eliminating cyber threats.
Considering the massive costs of data breaches, both on operations and finances, it’s well worth investing your resources in acquiring AI-powered cyber solutions for maximum protection against all types of cyber threats.


